We released our first version of the iO Store in February this year and have had good adoption and loads of interest from the community. One of the key features we made available as part of the App development tools, is the ability to cryptographically sign Links and Forms using a canonical algorithm that we documented here.
The algorithm uses HMAC SHA256 cryptographic hashes, seeded with a secret that App developers provide, to create links and forms that can be verified at destination systems. This provides the ability to do things like SSO and/or mitigate malicious tampering in transit. The feature has been used fairly widely and through this usage we have had a some useful feedback. We have taken this feedback on board and have just released improved documentation and a new reference implementation that removes some of the quirks in the previous implementation.
New Algorithm IO2-HMAC-SHA256
The previous algorithm identified by IO1-HMAC-SHA256 has now been deprecated in favor of the improved version IO2-HMAC-SHA256. Just to be clear, none of the issues we resolved were security issues or resulted in vulnerabilities. The fundamentals of the algorithm remain the same and there is no new technique to understand in order to use it.![]()
Key changes in the algorithm
- base64 encoding has been replaced with Hex encoding. Hex encoding, albeit results in a larger output, provides better Url safety.
- Removed an instance of double encoding which was unnecessary and added bloat.
I'm using the previous algorithm, what do I need to do?
If you are currently using pre-signed links you MUST update your App(s), that use these links, to specify the algorithm that they intend to use. The algorithm identifier is not currently required, and if not provided, will default to IO1-HMAC-SHA256. This will change on the 30th of April to default to IO2-HMAC-SHA256. Support will remain for the previous algorithm until the 29th June 2018 before support for it will be removed entirely.
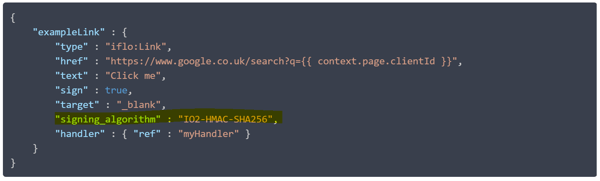
To specify the algorithm identifier, please add a property "signing_algorithm" to any extensions that specify "sign" as true. Then add the version you wish to support, as per the json snippet below:
Important: Any Apps that do not specify the signing_algorithm by the April 30th, but do currently rely on pre-signed links, will likely break after this date when the default value changes. Please specify an signing_algorithm ASAP. You must then switch to the new algorithm by June 29th 2018 or your App will likely break if it is using the old algorithm. If you do not use pre-signed links you have nothing to do.
Are there any reference implementations?
We have created and open sourced a c# implementation of both algorithms under a permissive Apache 2.0 license. Please feel free to use the code and submit issues and fixes if you find any. The code can be found on Github here.
In addition to the code we have also provided a nuget package for your convenience which you can pull into your own projects if you are using .Net. The package can be found at nuget.org (please use the latest version):
Further links:
More information can be found can be found at the following locations